7 Common Kubernetes Pitfalls (and How I Learned to Avoid Them)
It’s no secret that Kubernetes can be both powerful and frustrating at times. When I first started dabbling with container orchestration, I made more...
It’s no secret that Kubernetes can be both powerful and frustrating at times. When I first started dabbling with container orchestration, I made more...
Configuration is one of those things in Kubernetes that seems small until it's not. Configuration is at the heart of every Kubernetes workload. A miss...
Debugging Kubernetes control plane components can be challenging, especially when you need to quickly understand the runtime state of a component or v...
The release of Kubernetes 1.35 introduces a powerful new feature that provides a much-requested capability: the ability to trigger a full, in-place re...
The PersistentVolume node affinity API dates back to Kubernetes v1.10. It is widely used to express that volumes may not be equally accessible by all...
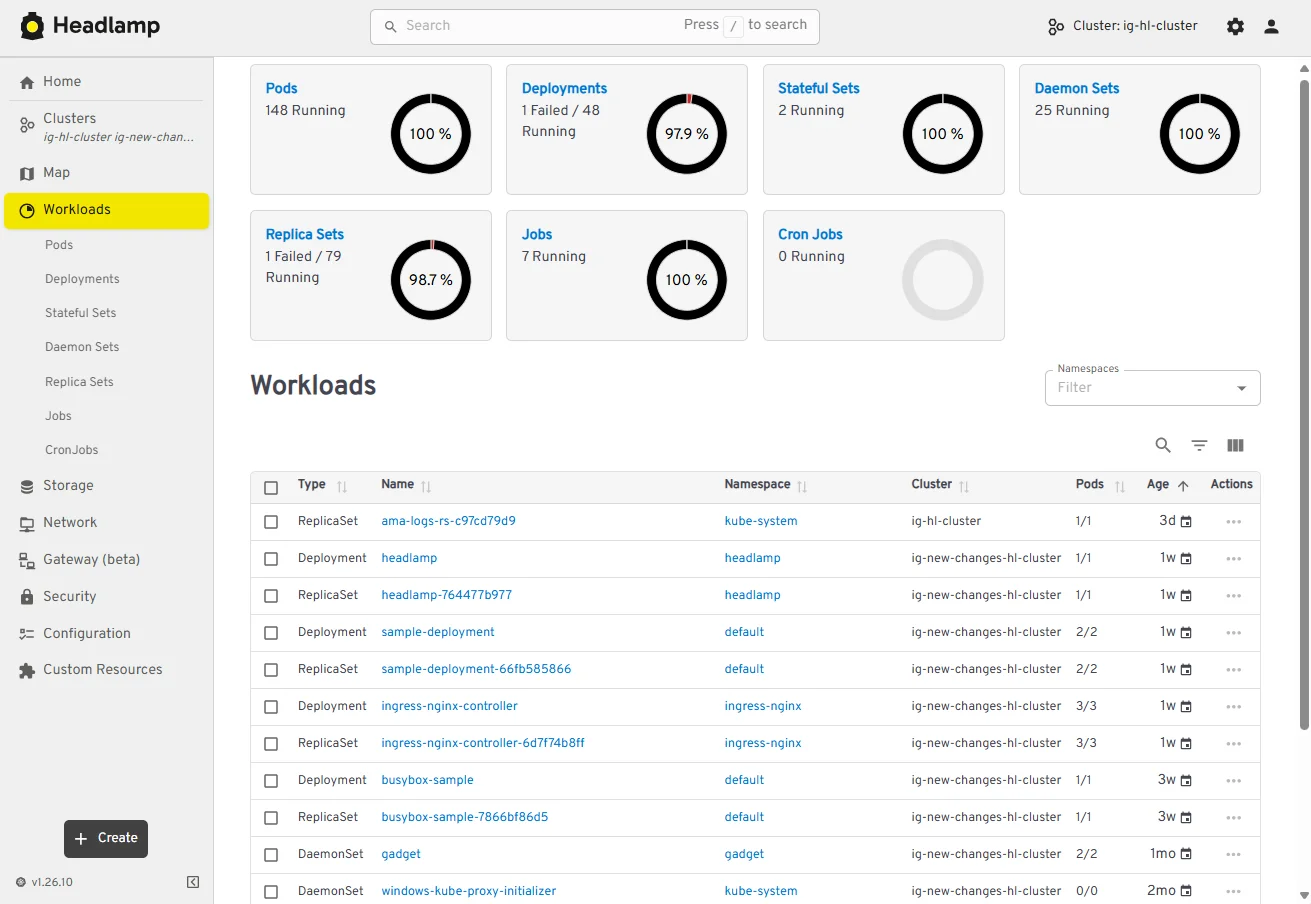
This announcement is a recap from a post originally published on the Headlamp blog. Headlamp has come a long way in 2025. The project has continued to...
Cluster API brings declarative management to Kubernetes cluster lifecycle, allowing users and platform teams to define the desired state of clusters a...
This document will guide you through setting up a local experimental environment with Gateway API on kind. This setup is designed for learning and tes...
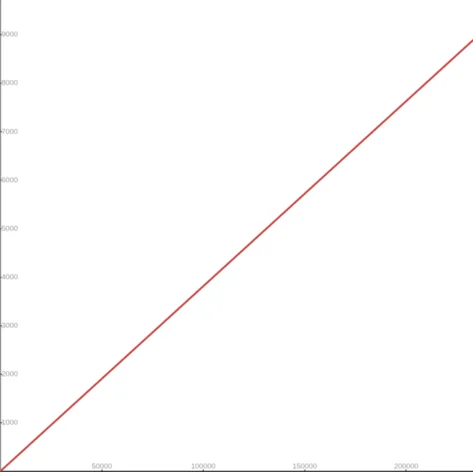
I'm excited to announce the implementation of an improved conversion formula from cgroup v1 CPU shares to cgroup v2 CPU weight. This enhancement addre...
In the standard Kubernetes model, a node’s suitability for workloads hinges on a single binary "Ready" condition. However, in modern Kuberne...
As announced November 2025, Kubernetes will retire Ingress-NGINX in March 2026. Despite its widespread usage, Ingress-NGINX is full of surprising defa...
The community around Kubernetes includes a number of Special Interest Groups (SIGs) and Working Groups (WGs) facilitating discussions on important top...

Bitcoin is up about 7% from the Sunday lows, even as equities and gold tread water. Analysts point to seller exhaustion, shifting gold correlation and...
At the center of the dispute is how far AI models should be allowed to go inside military systems.
Google has patched 129 Android vulnerabilities, including an actively exploited flaw in a widely used Qualcomm component.
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
This week on the Lock and Code podcast, we speak with Matthew Guariglia about Ring smart doorbells and the surveillance network they create.
The quiz is just bait. The real goal is to win permission to send browser notifications that can later be used for ads, scams, or shady promotions.
A suspected breach of the FBI’s wiretap network has investigators asking whether a nation-state was involved.
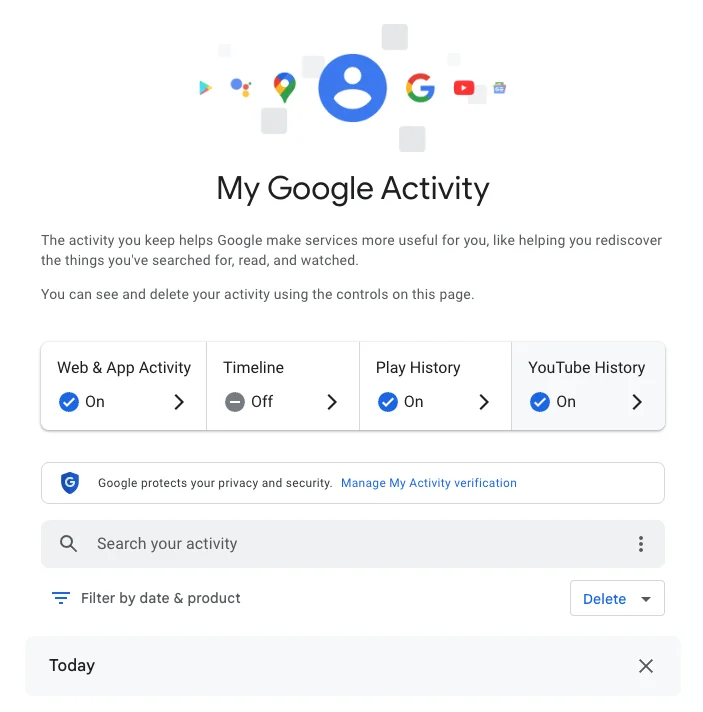
Google knows a lot about you. Here's how to check your Google Search history and how to prevent future tracking.