Attackers abuse OAuth’s built-in redirects to launch phishing and malware attacks
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
Reports of a "Great British Firewall" are exaggerated. And even if they wanted to, here's why it would be virtually impossible.
Google has urged the justices to strike down the controversial warrants, which can sweep up location data from hundreds of phones near a crime scene.

We uncovered a fake CleanMyMac site delivering SHub Stealer, a macOS infostealer that steals credentials and silently backdoors crypto wallets.
Bing search results pointed victims to GitHub repositories claiming to host OpenClaw installers, but in reality they installed malware.
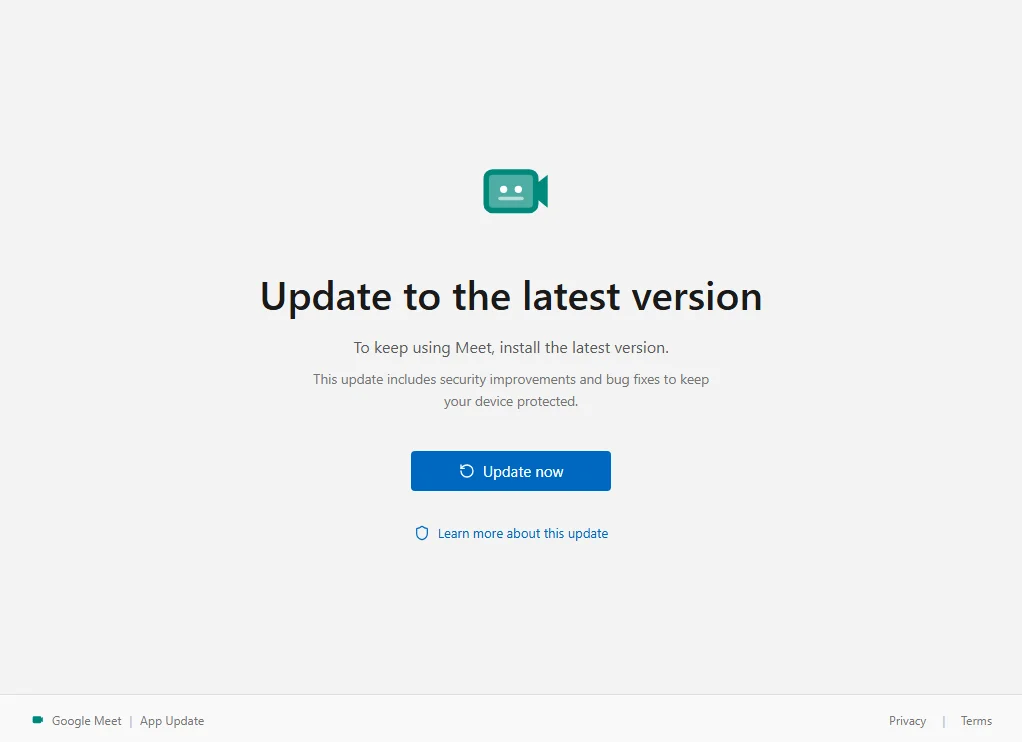
We found a fake Google Meet update that enrolls the victim's Windows PC in an attacker's device management system.
This week on the Lock and Code podcast, we speak with Matthew Guariglia about Ring smart doorbells and the surveillance network they create.
The quiz is just bait. The real goal is to win permission to send browser notifications that can later be used for ads, scams, or shady promotions.
Researchers uncovered fake Claude Code install pages spreading infostealers that steal passwords and browser sessions.
A suspected breach of the FBI’s wiretap network has investigators asking whether a nation-state was involved.
Dutch intelligence warns that attackers are hijacking Signal and WhatsApp accounts by tricking users into sharing verification codes or linking a mali...
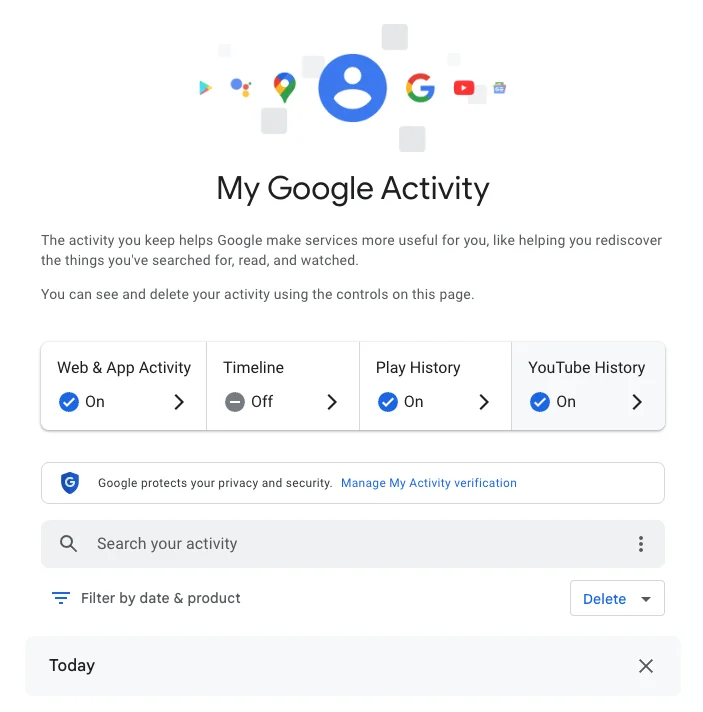
Google knows a lot about you. Here's how to check your Google Search history and how to prevent future tracking.
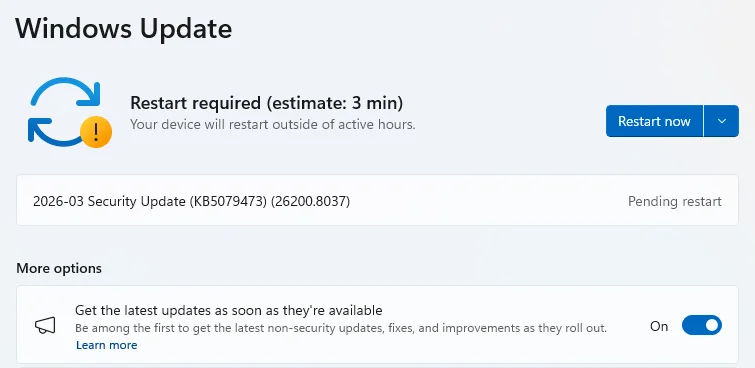
Microsoft patched 79 security vulnerabilities this month, including bugs that could let attackers escalate privileges or crash critical services.
Scammers are targeting Americans with robocalls during tax season. Here’s how to spot the scam.
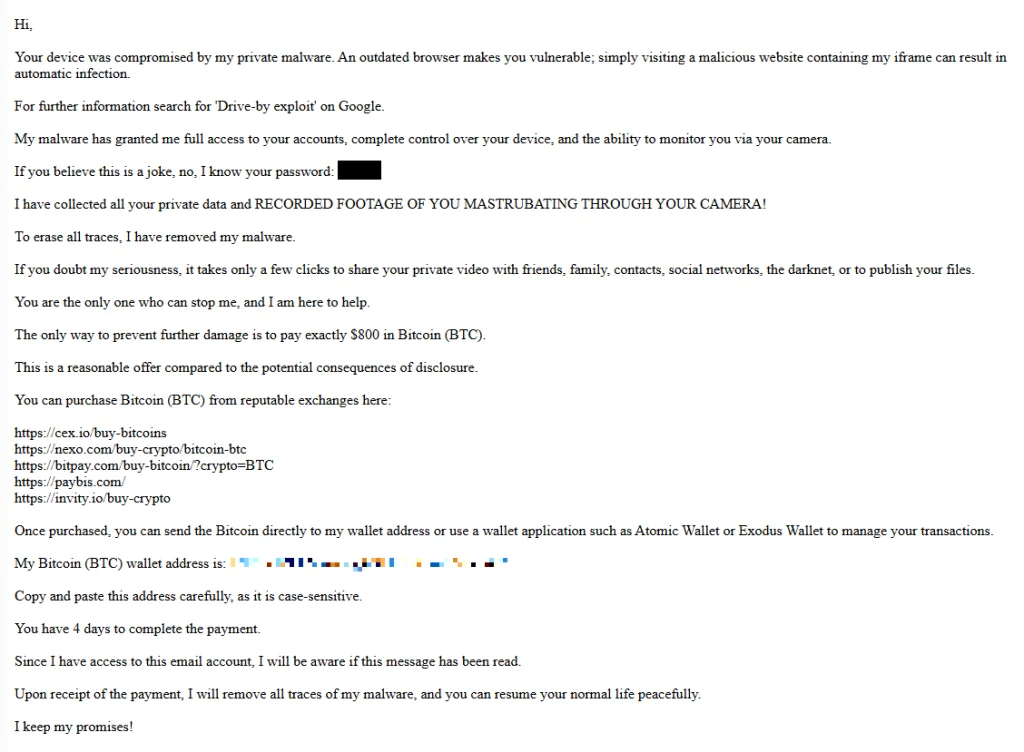
“You pervert, I recorded you!” sextortion emails include real passwords harvested from public temporary email inboxes.

Don't be fooled by the cheaper price, the Nothing Headphone A cover all the bases.

This is the first smartwatch to not tell me to sleep less because of its overestimations.

The affordable Pixel gets even cheaper at Best Buy.

My kingdom for a tighter primary camera.

This isn't the Google foldable I was hoping for.