Getting to the bottom of TMLE: forcing the target to behave
In the last couple of posts (starting here), I’ve tried to unpack some of the ideas that sit underneath TMLE: viewing parameters as functionals of a d...
In the last couple of posts (starting here), I’ve tried to unpack some of the ideas that sit underneath TMLE: viewing parameters as functionals of a d...
We are releasing the first version of Leptodon, our Leptos UI toolkit, into the wild. This release of Leptodon contains UI components for general appl...
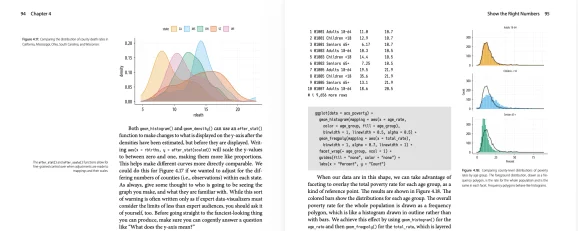
I’ve spent the last couple of months revising my Data Visualization book for a second edition that, ideally, will appear some time in the next twelve...
In a previous post, I described how to run a session to teach R to cell biologists. In this post we’ll look in a bit more detail at one of the steps:...
Formula 1 is one of the most compelling areas for data analysis in R because it combines structured results, lap-by-lap timing, pit strategy, and driv...

The patentsview R package was created by Chris Baker to simplify interactions with the PatentsView API as announced in Chris’ blog post in 2017. The A...

You can read the original post in its original format on Rtask website by ThinkR here: Sharing data across shiny modules, an update Some people have r...
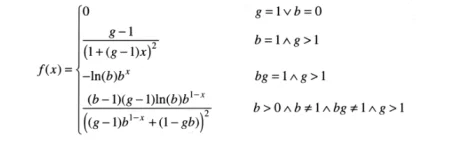
The MBBEFD Distribution After two years, the MBBEFDLite package for R is finally mature! As a brand-new actuary, in my first job, I had the privilege...

More than 85 partners will work with Mastercard to connect on-chain payments with banks, merchants and global commerce as part of the payment giant's...
The pool is designed for institutional and public company miners, focusing on compliance and regulated infrastructure.
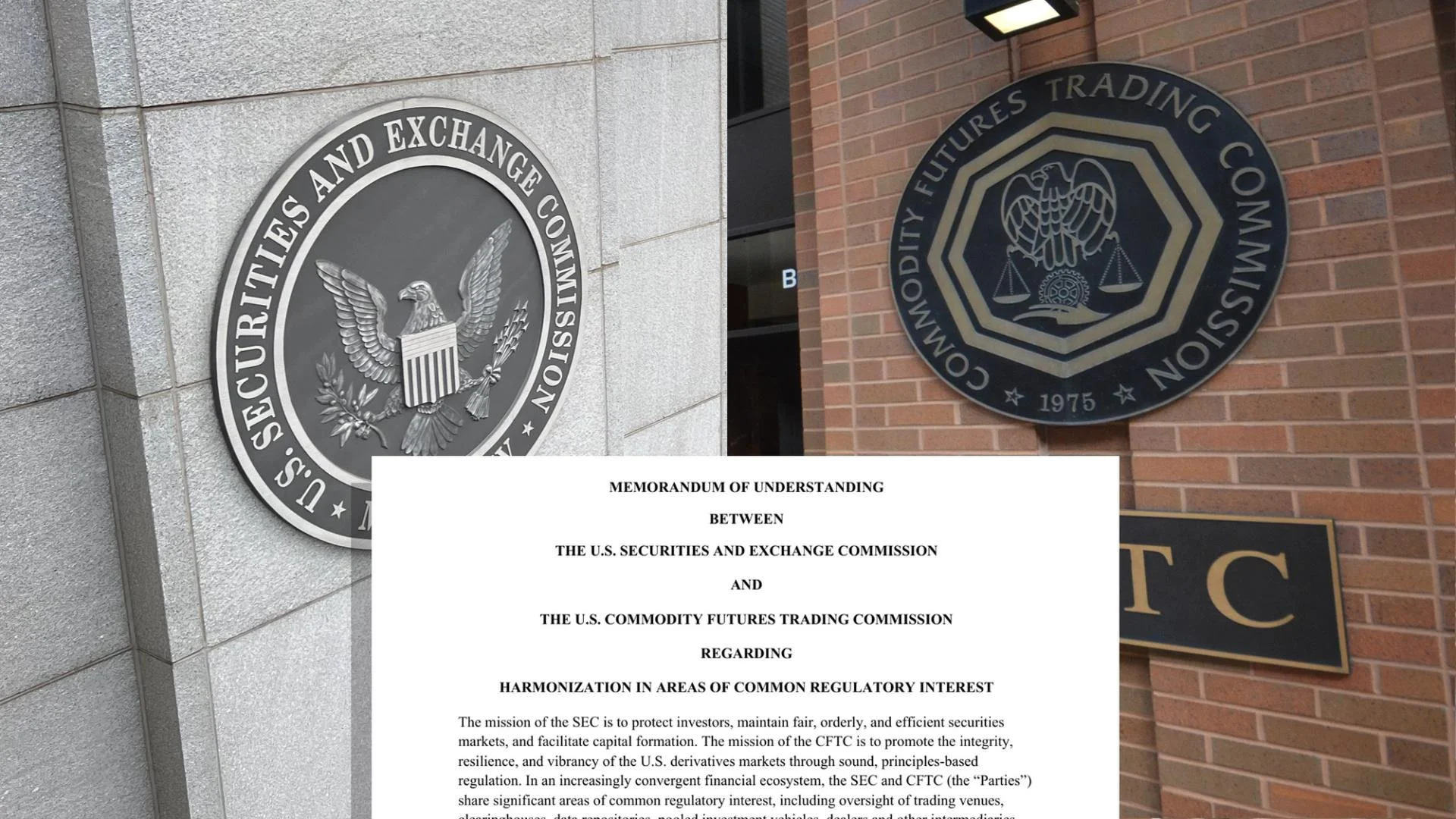
The two agencies sealed their memorandum of understanding to link the parts of their work that overlap, and coordinated crypto oversight is among the...
At the center of the dispute is how far AI models should be allowed to go inside military systems.
Google has patched 129 Android vulnerabilities, including an actively exploited flaw in a widely used Qualcomm component.
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
Reports of a "Great British Firewall" are exaggerated. And even if they wanted to, here's why it would be virtually impossible.
Google has urged the justices to strike down the controversial warrants, which can sweep up location data from hundreds of phones near a crime scene.

We uncovered a fake CleanMyMac site delivering SHub Stealer, a macOS infostealer that steals credentials and silently backdoors crypto wallets.
Bing search results pointed victims to GitHub repositories claiming to host OpenClaw installers, but in reality they installed malware.
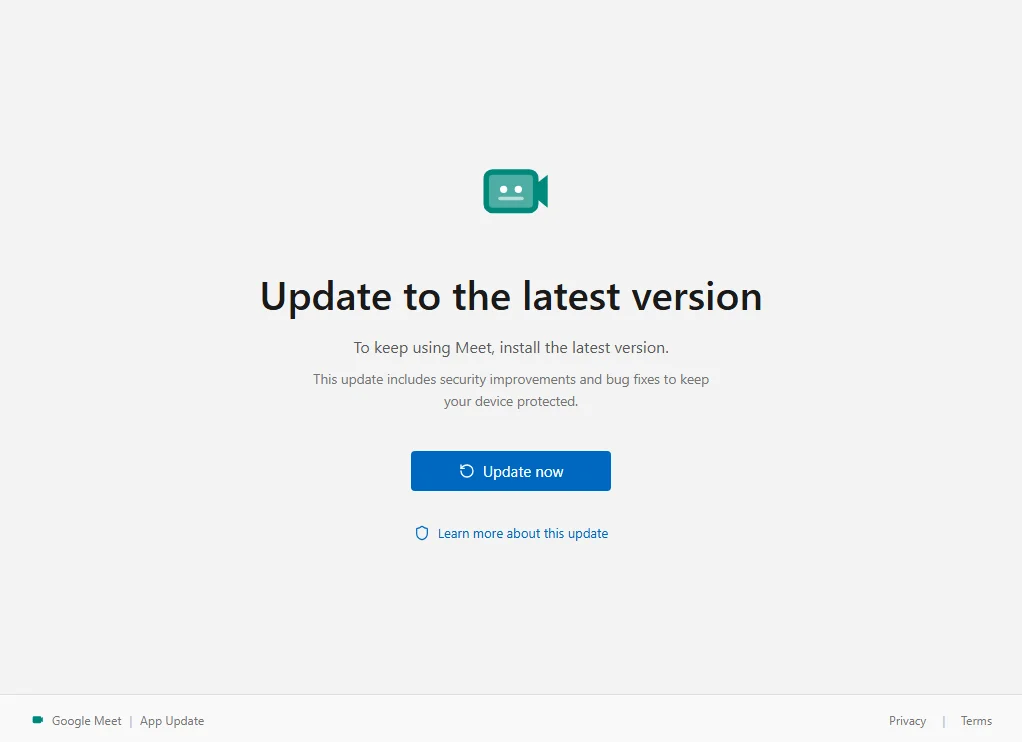
We found a fake Google Meet update that enrolls the victim's Windows PC in an attacker's device management system.
Researchers uncovered fake Claude Code install pages spreading infostealers that steal passwords and browser sessions.